Drupal Security Updates and Panama Papers

The amount of data leaked in the Panama Papers hack has proven monumental but what's alarming for all businesses is how the information was extracted from the Panamanian law firm Mossack Fonseca: the data was most likely taken by exploiting a security flaw from one of the firm’s outdated systems. Open source systems can be exploited if known security flaws aren't patched within a reasonably quick turnaround time, and in the case of the Panama Papers, there were almost too many holes in the security dam.
This is where a firm like Mossack Fonseca probably wishes that they'd invested the time and effort to keep their systems up to date.
Security experts have gone on record to decry the law firm’s outdated practices. The seasoned eyes and minds of a well-organized team of security experts could have applied patches to known vulnerabilities and lobbied Mossack Fonseca to communicate sensitive account information in more secure manners.

A Panama City-based law firm was at the heart of the largest data breach in history. Photo courtesy of Flickr user Brian Gratwicke
Panama Papers By The Numbers
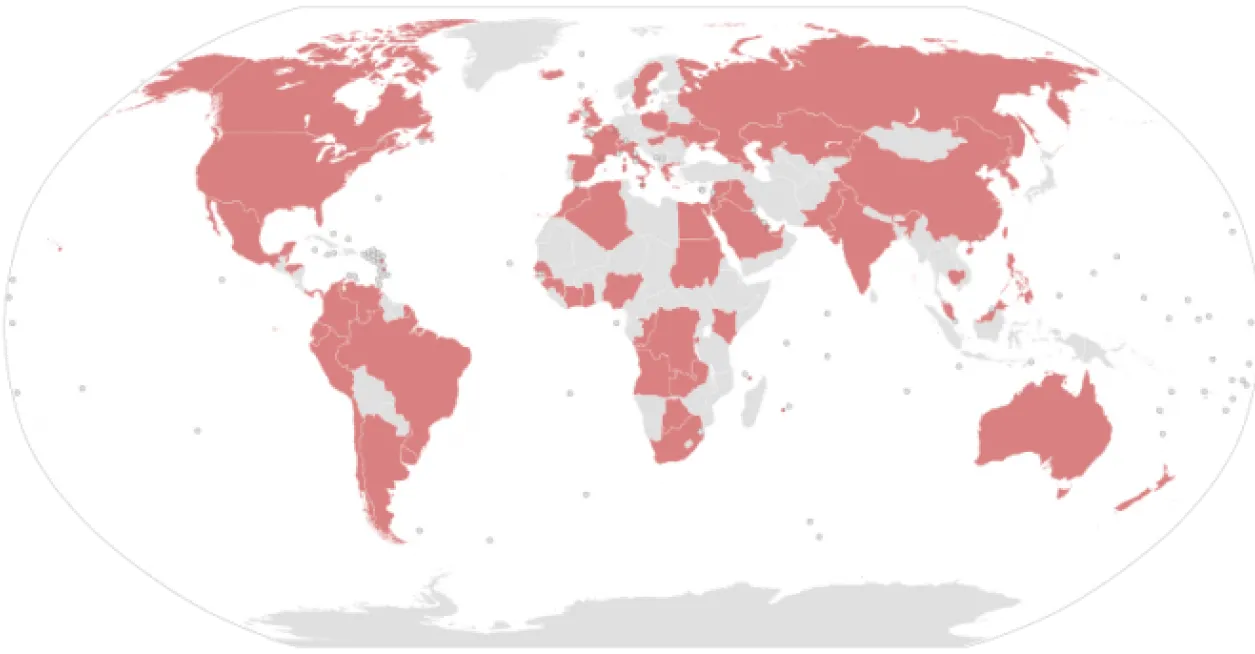
The leak includes more than 4.8 million emails, 3 million database files, and 2.1 million PDFs taken from the Panamanian law firm’s servers.
Altogether there were 2.6 terabytes of data, a thousandfold larger than the infamous WikiLeaks Cablegate leak of 2010 and the largest data breach in history.
More than 400 journalists worked together to collect and analyze 11.5 million documents that were shipped from anonymous sources.
Journalists who coordinated the reporting on the so-called Panama Papers communicated with the source who leaked the documents over various encrypted messaging services.
The journalists then worked with the source material in a search engine that was built by developers from the International Consortium of Investigative Journalists, or ICIJ. The Washington, D.C.-based ICIJ allowed limited access to the documents and their searchable database via two-factor authentication, the common protection standard that many consumers use to protect a personal email or social network account.
How All the Data Leaked
Forbes identified Drupal 7.23 as the CMS that powered Mossack Fonseca’s client-facing information portal. More than two dozen known security issues face sites running on that version of Drupal, and historical logs of Mossack Fonseca's site point to 2013 as the most recent security update. Some of those lingering security vulnerabilities could allow users to gain access to sensitive information and execute malicious code on servers. Additionally, the firm’s main website is running on a version of the open source WordPress platform that’s more than three months out of date. The email systems used by the firm weren’t encrypted either, and Transport Layer Security (TLS) is seen as at least basic security protocol in today’s digital landscape.
If you have never heard about those encryption tools, they are designed to provide communications security over a computer network. Add up all the weak points in Mossack Fonseca’s security protocols and it allows for numerous theories on how the data were leaked.
If Mossack Fonseca had been regularly updating their systems and patching security issues, many of these routes would have been closed to hackers. What’s most surprising is that, in the wake of 2014’s “Drupalgeddon” incident, the team responsible for security at Mossack Fonseca didn’t take measures to toughen security.

Open Source Tools - A Tale of Do’s & Don'ts
In an ironic twist, all of the data was probably originally taken by exploiting a crop of outdated open source systems, then it was steadily analyzed and prepared for release on another patchwork of free and open source systems. The search engine built by IDIJ indexed data from the leaked documents with Apache TIKA and made it searchable with Apache SOLR. Both of these are leading open source tools for indexing and searching site data, but in this case, they were used to search terms connected to the secretive financial dealings of world leaders and major corporations.
On the one hand, there was a company which touted their respect for client privacy and security — Mossack Fonseca — and the other a consortium of journalists who’ve witnessed one epic data leak after another. Sometimes the journalists have been caught flat-footed by the leaks, such as WikiLeaks’ practice of disseminating troves of leaked information all at once, and at other junctures, they’ve been the ones guiding the release of information to the public, as they did with the Edward Snowden leaks and here with the Panama Papers.
One thing is clear: the world has come a long way from an era when whistleblowers had to clandestinely photo-copy documents or handoff briefcases in shadowy locations. Tools such as encrypted messaging systems are now facilitating the secure exchange of information across great distances. It’s an advantage that can swing to a group’s favor, as it did for the journalists working to publish stories about the Panama Papers, and one that can go against organizations with sensitive data that they need to protect.
At the very least, Promet Source recommends securing sites with SSL or TSL protocols. Two-factor authentication, the system that allowed a global group of media professionals to access the leaked data, is another good starting point for securing access to sensitive information. Proactively applying updates to sites whenever a new security release is available is a critical habit to adopt, as evidenced by the Panama Papers hack, and one that Promet employs for its clients.
If you have sensitive data that you need to keep secure -- and hopefully not in service of shadowy tax avoidance schemes -- then get in touch with Promet Source and learn the ropes of open source the secure way!
Other Insights & Resources you may like
Get our newsletter
Get weekly Drupal and AI technology advancement news, pro tips, ideas, insights, and more.