Drupal Development Services
Trusted by the public sector. Built on Drupal. Powered by Promet.
When your user base grows, your website can’t just keep up—you have to lead. That’s where Promet Source comes in. With two decades of open-source leadership and a deep bench of public sector expertise, we help you leverage the full power of Drupal to deliver secure, accessible, and future-ready digital experiences.
Whether you’re supporting millions of residents or streamlining complex services across departments, we develop scalable Drupal solutions tailored to your size, structure, and strategic priorities.

Enterprise-Grade Architecture, minus the Vendor Lock-in
Large public entities need more than templates. You need a CMS that:
- Adapts to complex organizational workflows
- Integrates cleanly with your internal systems and apps
- Supports multi-site governance and granular permissions
- Meets accessibility and security standards across the board
That’s Drupal. And no one brings out its best in the public sector like Promet.
Drupal Development Services vs. Provus®Gov, Provus®Edu, and DUSWDS
Promet Source proudly offers a suite of pre-packaged Drupal solutions—Provus®Gov for small-to-mid-sized municipalities, Provus®EDU for higher education, and DUSWDS for federal websites.
Our custom Drupal Development Services are specifically designed for larger government and higher education organizations seeking deep customization, advanced integrations, and strategic partnership. Unlike our pre-packaged solutions, our tailored Drupal platforms give you full control to address your unique challenges:
- Customized, complex workflows tailored to your organizational structure
- Custom integrations requiring advanced technical architecture
- Unique design and user experience demands beyond out-of-the-box what Provus®Gov offers
- Robust scalability for large user bases and high traffic volumes
Why Promet for Enterprise Drupal Development
Our Drupal team brings deep experience solving the faced by large public sector websites. Whether you manage multiple departments, require seamless system integrations, or prioritize stringent accessibility and compliance standards, we build custom solutions designed for your operational reality.

We don’t tack on accessibility. We integrate it into our development of your website. Every Drupal site we build meets or exceeds WCAG 2.1 AA standards—because your digital services should be usable by everyone.

Whether you need us to integrate GIS, CRM, legacy systems, or third-party platforms, our Drupal developers can do it for you to ensure your website is connected to the rest of your tech stack.
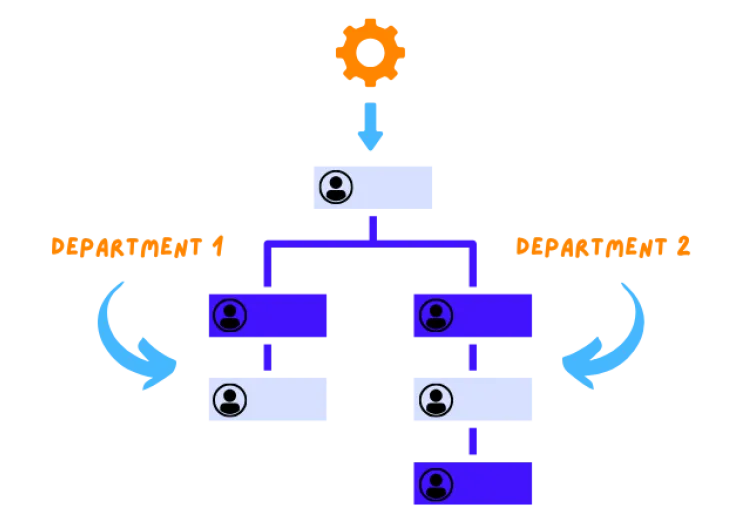
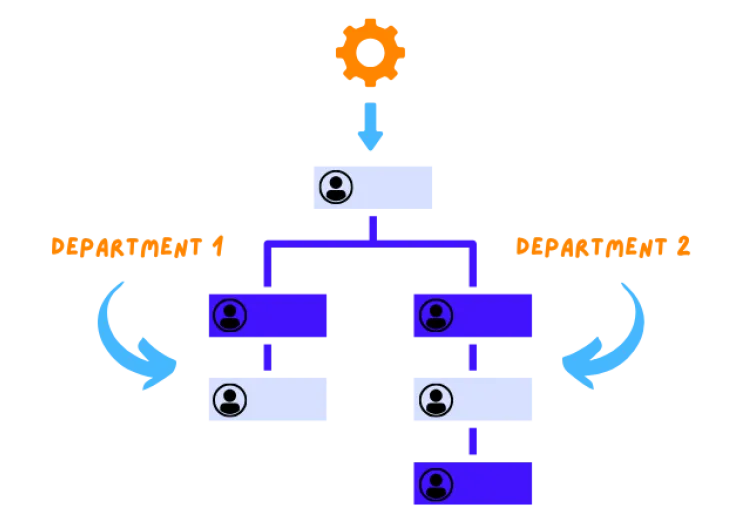
We build publishing workflows and role-based permissions that match your content governance needs—so the right people have the right access at the right time.
Our Drupal team brings deep experience solving the faced by large public sector websites. Whether you manage multiple departments, require seamless system integrations, or prioritize stringent accessibility and compliance standards, we build custom solutions designed for your operational reality.
We don’t tack on accessibility. We integrate it into our development of your website. Every Drupal site we build meets or exceeds WCAG 2.1 AA standards—because your digital services should be usable by everyone.
Whether you need us to integrate GIS, CRM, legacy systems, or third-party platforms, our Drupal developers can do it for you to ensure your website is connected to the rest of your tech stack.
We build publishing workflows and role-based permissions that match your content governance needs—so the right people have the right access at the right time.


Featured Projects
Learn how Promet Source made a website for the Southern Illinois University School of Medicine to serve users and reflect the school's role in the region.
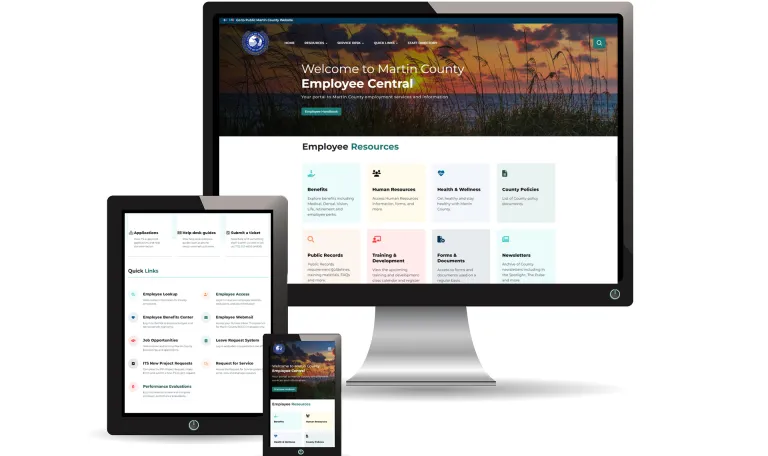
See how Promet Source transformed the Martin County, FL employee intranet, with a distinguished user experience for a more efficient channel for sharing internal information.
FAQ's
Absolutely. Drupal is renowned for its flexibility and scalability, making it an ideal choice for sizable organizations. Our Drupal Development Services focus on understanding your workflows and customizing the platform to seamlessly integrate with your existing systems. Whether it's search features, patient portals, or payment processing, Drupal can handle it all.
Drupal offers robust search tools that can help users easily find information on your website. With our expertise in Drupal development, we can create a search experience that is fast, accurate, and intuitive. Your users will definitely feel satisfied when they effortlessly find the information they need, improving their overall experience with your website and organization.
Yes! Our development team thrives on creating custom modules for Drupal ecommerce websites to integrate complex systems into intuitive websites and mobile applications.
From payment options to ecommerce processes and third-party applications, we are an ecommerce web development company that builds flawless integrations to meet distinct project goals.
Sure thing! Feel free to fill out our contact form or connect with us through chat.